“We've spent 3 days combing through Apple documentation just to still be lost, We don't want our app to get rejected”
Apple require us to implement Sign in with Apple latest by 30th June 2020. And yet the documentation is severely lacking, what should we do after getting user data from Sign in with Apple on iOS side? What does the error message like invalid_client even mean? You start to worry what if you couldn’t implement Sign in with Apple before the deadline, and Apple rejected your app upcoming update, causing the delay of some fixes/updates to your app, which makes your users and your boss unhappy 😣.
“I have wasted so much time trying to solve the error, the error message isn't even helpful!”
You have followed a tutorial on how to implement Sign in with Apple step by step, but you are stuck at the dreaded “invalid_client” or "invalid_grant" error every time you try to validate the authorization code with /auth/token.
Alright, I know it tells me the client is invalid... then what should I do to fix this?!
You checked your client_id, client_secret and even the redirect_uri parameters, all of them seem correct, then you try to swap client_id with the app bundle ID, web services ID, changing the headers used to generate the client secret JWT… hours has passed and despite all the trial and error, you are still getting the same “invalid_client” error! 🤬
The error message “invalid_client” isn’t particularly helpful as it doesn’t say which part of your code is wrong, could it be your client_id? client_secret? or could it be the authorization code that you’ve gotten from the app isn’t formatted properly? You wished Apple would provide a more helpful error message on solving the issue.
"Much of the documentation for Sign in with Apple ignores the server-side implementation. After struggling for ages, I came across Practical Sign in with Apple which helped me implement Sign in with Apple in a matter of days. The best part is that the server-side code is in multiple languages! I would highly recommend this book if you've been struggling with Sign in with Apple - it's a bargain!"
- Nic Morris
“I have scoured all the documentation at length and have still not gotten anywhere.”
After spending countless hours battling the token validating issue, you have finally managed to retrieve the token! yay! But now you are stuck again, as there isn’t even a word in Apple documentation on how to handle subsequent REST API call after user has signed in successfully! As the token returned from validating authorization code is just valid for 10 minutes, and Apple only allow refreshing token once a day (more than that will result in throttling), how should we handle subsequent REST API call to the backend using token?
There’s an endpoint to get Apple public key, but how do I even use this hash to verify signature?! This certainly doesn’t look like a public key file format (eg: —–BEGIN PUBLIC KEY—– xxxxxx —–END PUBLIC KEY—– ) :
{
"keys": [
{
"kty": "RSA",
"kid": "AIDOPK1",
"use": "sig",
"alg": "RS256",
"n": "lxrwmuYSAsTfn-lUu4goZSXBD9ackM9OJuwUVQHmbZo6GW4Fu_auUdN5zI7Y1dEDfgt7m7QXWbHuMD01HLnD4eRtY-RNwCWdjNfEaY_esUPY3OVMrNDI15Ns13xspWS3q-13kdGv9jHI28P87RvMpjz_JCpQ5IM44oSyRnYtVJO-320SB8E2Bw92pmrenbp67KRUzTEVfGU4-obP5RZ09OxvCr1io4KJvEOjDJuuoClF66AT72WymtoMdwzUmhINjR0XSqK6H0MdWsjw7ysyd_JhmqX5CAaT9Pgi0J8lU_pcl215oANqjy7Ob-VMhug9eGyxAWVfu_1u6QJKePlE-w",
"e": "AQAB"
}
]
}Enough complain about Apple, let’s pause a moment and imagine....
What if you could implement Sign in with Apple within a day, submit the app update to App Store confidently and continue on with your feature implementations / bug fixes?
Wouldn’t it be nice if there’s a straightforward, step-by-step guide which you can follow to implement Sign in with Apple? From generating public key, validate authorization code, validating and parsing identityToken to subsequent REST API calls between your iOS app to your server?
You could implement Sign in with Apple within a day, and continue working on features or bug fixes that matters, which make your users happier (and also your boss).
Follow a step by step guide with code sample on each step to implement Sign in with Apple, with Practical SIWA guide book

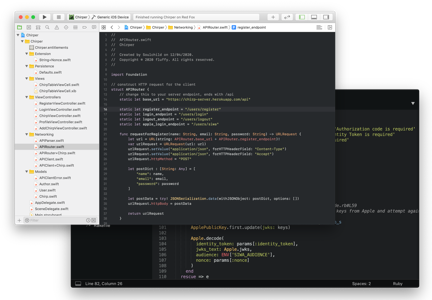
The book will show the overall flow of Sign in with Apple, and explain each of steps from retrieving authorizationCode from iOS app, to generating client secret, to overview of your own access token generation strategies. All of the backend steps involved with Sign in with Apple comes with sample code in Ruby, PHP, Python and NodeJS.
This book is focused on practical steps (using libraries for handling cryptography and decoding, instead of explaining theory and rolling your own), concisely written to help you finish implement the whole Sign in with Apple flow as quickly as possible, so you can move on to implement those really important features / fixes.
Just wanted to give a shoutout to you for writing this book. We spent 3 days combing through Apple docs just to still be lost. Your book helped guide our small team of developers @DiagnosUs to implement SIWA! Cheers
— Simon Pacheco (@simonpac_) June 25, 2020
What's in the book?
Annotation: 🔋 = this chapter comes with sample code in Ruby, PHP, Python and NodeJS.Here's the table of contents of the book :
- Big picture of the Sign in with Apple flow
- What is JSON Web Token (JWT), how to decode and debug them, and libraries recommendation (🔋)
- Sign in with Apple implementation on iOS side, how to retrieve user data and check if user has logged in / out
- How to retrieve Apple's public keys, and use it to verify the identityToken and decode it (🔋)
- How to validate the authorizationCode retrieved from iOS app (🔋)
- How to use private key to generate client secret, and use this client secret to exchange access token by calling Apple's endpoint (🔋)
- How to refresh access token using Apple's endpoint (🔋)
- Overview of strategies you can use to generate your own access token for authentication between your app to your server API
- How to implement Sign in with Apple on your web app frontend
- How to implement Sign in with Apple on other platforms
- How to send email to private relay email (user who choose to hide their real email address will get a randomly generated email address from Apple)
The Book + Demo App and Backend code
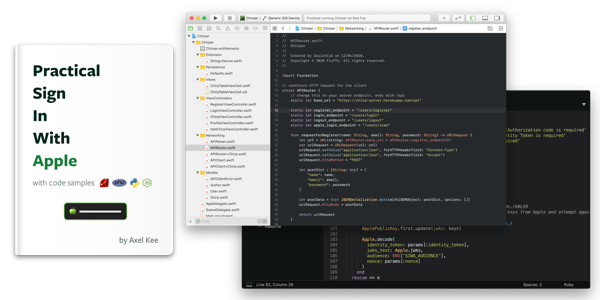
- The book in PDF format, 180 pages
- You can finish the book and implement Sign in with Apple flow within a day
- Code examples for each of the steps (In Ruby, PHP, Python, NodeJs), you can copy paste them and just change the variables as needed
- Functional demo iOS app code (Swift 5, Xcode 11.3) with accompanying backend code written in Ruby, which you can study and deploy the backend code to Heroku directly, and run the iOS app.
- Demo includes the full Sign in with Apple flow, your server's own email/password login mechanism, and your server generate its own access token for communication between the app with your server API.
Just the Book

- The book in PDF format, 180 pages
- You can finish the book and implement Sign in with Apple flow within a day
- Code examples for each of the steps (In Ruby, PHP, Python, NodeJs), you can copy paste them and just change the variables as needed
Functional demo iOS app code (Swift 5, Xcode 11.3) with accompanying backend code written in Ruby, which you can study and deploy the backend code to Heroku directly, and run the iOS app.Demo includes the full Sign in with Apple flow, your server's own email/password login mechanism, and your server generate its own access token for communication between the app with your server API.
Just the Demo App and Backend code
The book in PDF format, 180 pagesYou can finish the book and implement Sign in with Apple flow within a dayCode examples for each of the steps (In Ruby, PHP, Python, NodeJs), you can copy paste them and just change the variables as needed- Functional demo iOS app code (Swift 5, Xcode 11.3) with accompanying backend code written in Ruby, which you can study and deploy the backend code to Heroku directly, and run the iOS app.
- Demo includes the full Sign in with Apple flow, your server's own email/password login mechanism, and your server generate its own access token for communication between the app with your server API.
Can I try a free sample?
Absolutely! I understand that it's hard to know whether a book you found online will actually help. You can download the 2 free sample chapters plus table of contents, and see if it's right for you
Just wanted to give a shoutout to you for writing this book. We spent 3 days combing through Apple docs just to still be lost. Your book helped guide our small team of developers @DiagnosUs to implement SIWA! Cheers
— Simon Pacheco (@simonpac_) June 25, 2020
Guarantee
The reason I wrote this book is to help you to implement Sign in with Apple as soon as possible. If using this book does not help you learn and implement Sign in with Apple, let me know, within 30 Days of the date of your purchase, and I'll give you a complete refund. No argument. No risk. 100% guaranteed. You can contact me at axel@fluffy.es
Have any questions? Contact me at axel@fluffy.es, I'll be happy to answer.
"Much of the documentation for Sign in with Apple ignores the server-side implementation. After struggling for ages, I came across Practical Sign in with Apple which helped me implement Sign in with Apple in a matter of days. The best part is that the server-side code is in multiple languages! I would highly recommend this book if you've been struggling with Sign in with Apple - it's a bargain!"
- Nic Morris
About the Author
Hi, I'm Axel Kee. I’ve been developing iOS apps for companies, clients and myself — from small indie app (they cover my daily coffee money ☕️) to social app that get hundreds of thousands of downloads — since 2016.
I have been writing about iOS development stuff at my blog since 2018 as well.